Data loss represents one of the most severe operational risks to any digital infrastructure. Whether caused by hardware degradation, malicious ransomware deployments, or natural disasters, the sudden unavailability of critical data can cripple personal projects and enterprise workflows alike. Relying on a single storage drive or a basic cloud synchronization folder is fundamentally inadequate for true data resilience.
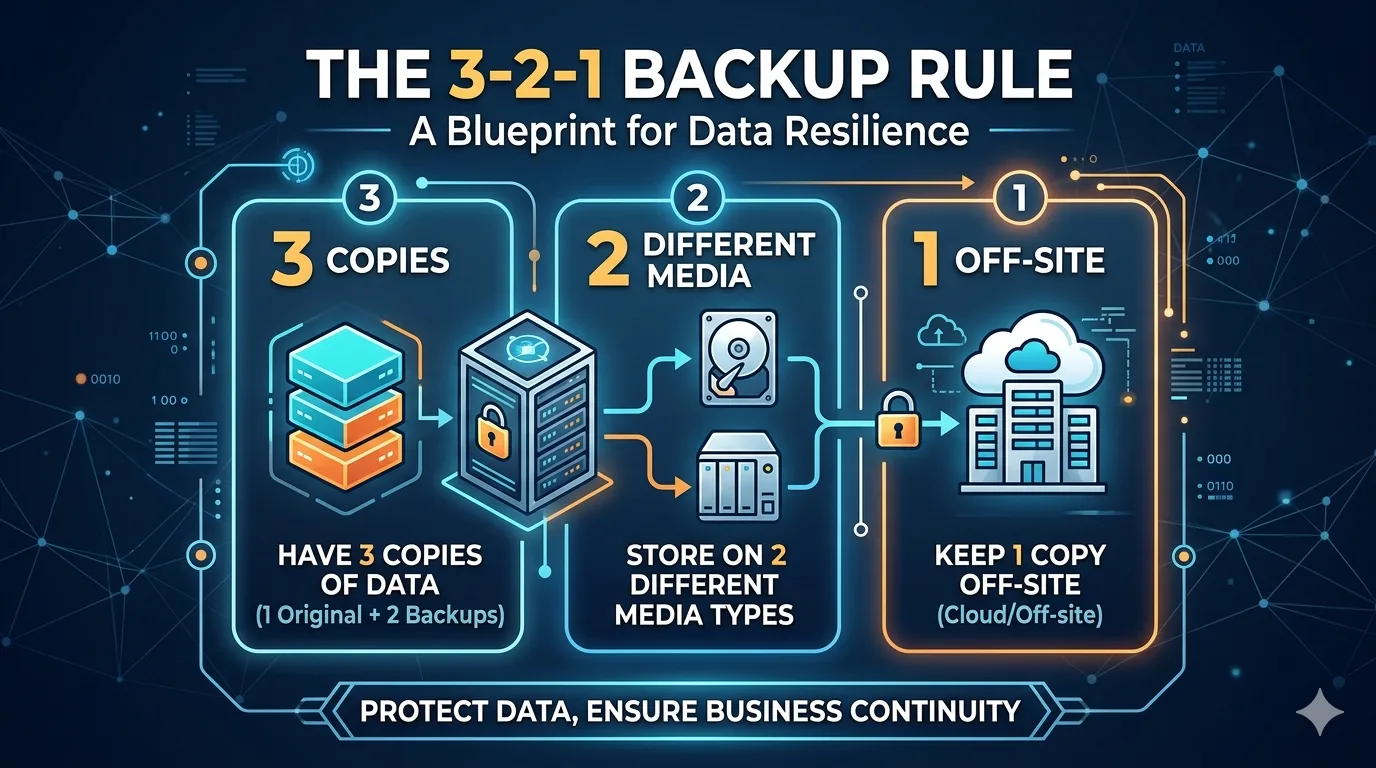
To establish a robust defense against catastrophic data loss, IT professionals and system administrators rely on a proven methodology: the 3-2-1 backup rule. This framework provides a systematic approach to redundancy, ensuring that your digital assets remain recoverable under almost any failure scenario.
Understanding and implementing this architecture is essential for anyone serious about information security. Here is a breakdown of how the 3-2-1 backup rule operates and how you can deploy it effectively.
Decoding the 3-2-1 Backup Architecture
The 3-2-1 rule is an industry-standard formula designed to eliminate single points of failure within your data storage environment. It breaks down into three distinct operational requirements.
Maintain 3 Copies of Your Data
The foundational principle dictates that you should possess three identical instances of your critical files. This includes your primary production data—the files you actively read and write daily—alongside two separate backup copies. Statistically, the probability of three independent storage locations failing simultaneously is exponentially lower than a dual-copy system.
Utilize 2 Different Media Types
Storing all three copies on the same type of hardware exposes your data to device-specific vulnerabilities. If you keep your backups on two identical internal hard drives, a localized power surge or a specific firmware bug could destroy both simultaneously.
To mitigate this, the framework requires spreading your backups across two distinct storage mediums. For instance, you might run your primary data on a local NVMe SSD, store the first backup on a Network Attached Storage (NAS) configured in a RAID array, and keep another backup on a high-capacity external HDD or optical media.
Keep 1 Copy Offsite
Physical proximity is a major risk factor in data security. A localized disaster—such as a fire, flood, or a targeted physical theft—can easily compromise your primary machine and your local backups at the same time.
The final mandate of the 3-2-1 rule is to isolate one backup copy in a remote location. Historically, this meant rotating physical tape drives to an offsite vault. Today, this is typically achieved by leveraging encrypted cloud storage platforms, such as AWS S3, Backblaze B2, or dedicated offsite server colocation.
Strategic Benefits of the 3-2-1 Framework
Adopting this systematic approach provides several immediate advantages for your data security posture:
- Comprehensive Redundancy: By diversifying your storage mediums and locations, you insulate your data against both logical corruption and physical hardware failure.
- Ransomware Mitigation: If a malicious encryption payload compromises your local network and attached drives, an isolated, offsite cloud backup (especially one utilizing immutable storage) remains untouched and fully recoverable.
- Rapid Disaster Recovery: Having a local backup ensures fast restoration for common data-loss events, while the offsite copy acts as an ultimate fail-safe for critical site-wide disasters.
Practical Tips for Implementation
Deploying the 3-2-1 rule requires more than just purchasing hardware; it requires ongoing operational discipline.
First, automate your backup processes. Relying on manual file transfers inevitably leads to human error and outdated backups. Utilize robust backup software that schedules automatic, incremental snapshots of your data to both your local NAS and your offsite cloud provider.
Second, rigorously verify your data integrity. A backup is only valuable if it can be successfully restored. Schedule periodic restoration drills to confirm that your files are uncorrupted and that your recovery protocols function as intended. Finally, ensure that your offsite data is secured with zero-knowledge encryption before it leaves your local network, protecting your privacy against potential breaches at the data center level.
Securing Your Digital Infrastructure
Hope is not a valid strategy for data protection. As digital environments become increasingly complex and threat vectors evolve, maintaining a resilient backup solutions architecture is a technical necessity. By systematically applying the 3-2-1 backup rule, you establish a fortified perimeter around your critical information, ensuring high availability and total peace of mind in the face of unpredictable hardware and security failures.