
How Advanced Security Platforms Improve Threat Detection and Response
Cyber threats rarely follow predictable patterns. As organizations expand across cloud environments, remote workforces,
Privacy, infosec, hacking, data protection, VPNs
331 articles
Cyber threats rarely follow predictable patterns. As organizations expand across cloud environments, remote workforces,

A cyber security and compliance strategy is a structured plan that aligns an organization's security controls with regul
When people think of security firms, the first image is often a uniformed guard at a gate or reception desk. That is onl

Opening the Gates: The Rising Stakes of Cybersecurity in 2026In early 2026, a startling cyberattack on a leading multina

Shadows of a New Era: The Unfolding Scene of 2026 HackingOn a brisk morning in March 2026, a coordinated cyberattack tar
Why Identity Governance Risk Starts With How Access Decisions Are Made Identity governance risk is not always visib
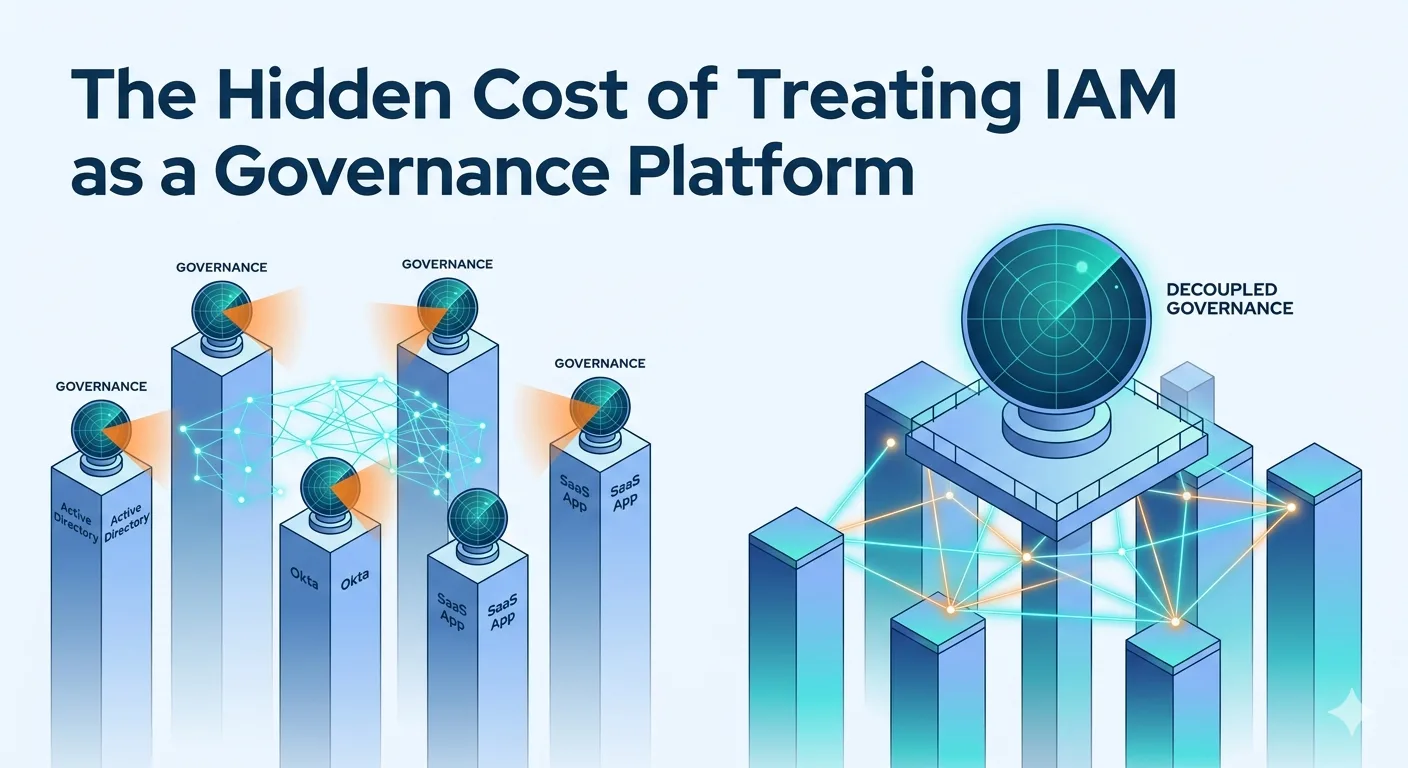
There is a quiet assumption embedded in how many enterprises approach identity security governance: that because IAM sys

The Invisible Battlefield: A Startling Reality CheckImagine waking up to find that your entire digital identity—the bank

Every small business that operates online is a target. Cybersecurity services for small businesses are no lon

When Expertise Falters: The Hidden Pitfalls Behind Hacking FailuresIn the shadowed corridors of cyberspace, where digita

Peering Into the Hacker’s Mind: The Digital Frontier of 2026In early April 2026, a sophisticated cyberattack targeted a

A Digital Crossroads: Privacy’s Critical MomentOn a quiet morning in early 2026, a major global social media platform di

Losing the keys to your vehicle is a visceral, stressful experience that leaves you feeling exposed. Now, consider that

When the Digital Frontier Became a BattlefieldIn early 2026, a global financial firm suffered a breach that was unlike a

IntroductionCyber security audit services in tirupati play a crucial role in today’s digital landscape where businesses

Unlocking the Power of Advanced VPN StrategiesImagine a digital fortress where your online identity, data, and activitie

Setting the Stage: A Glimpse into the Hacker's WorldIn 2026, the digital frontier has expanded exponentially, with over

Picture this: you've just unboxed a brand-new smart speaker, a set of automated blinds, or a wireless security camera, a
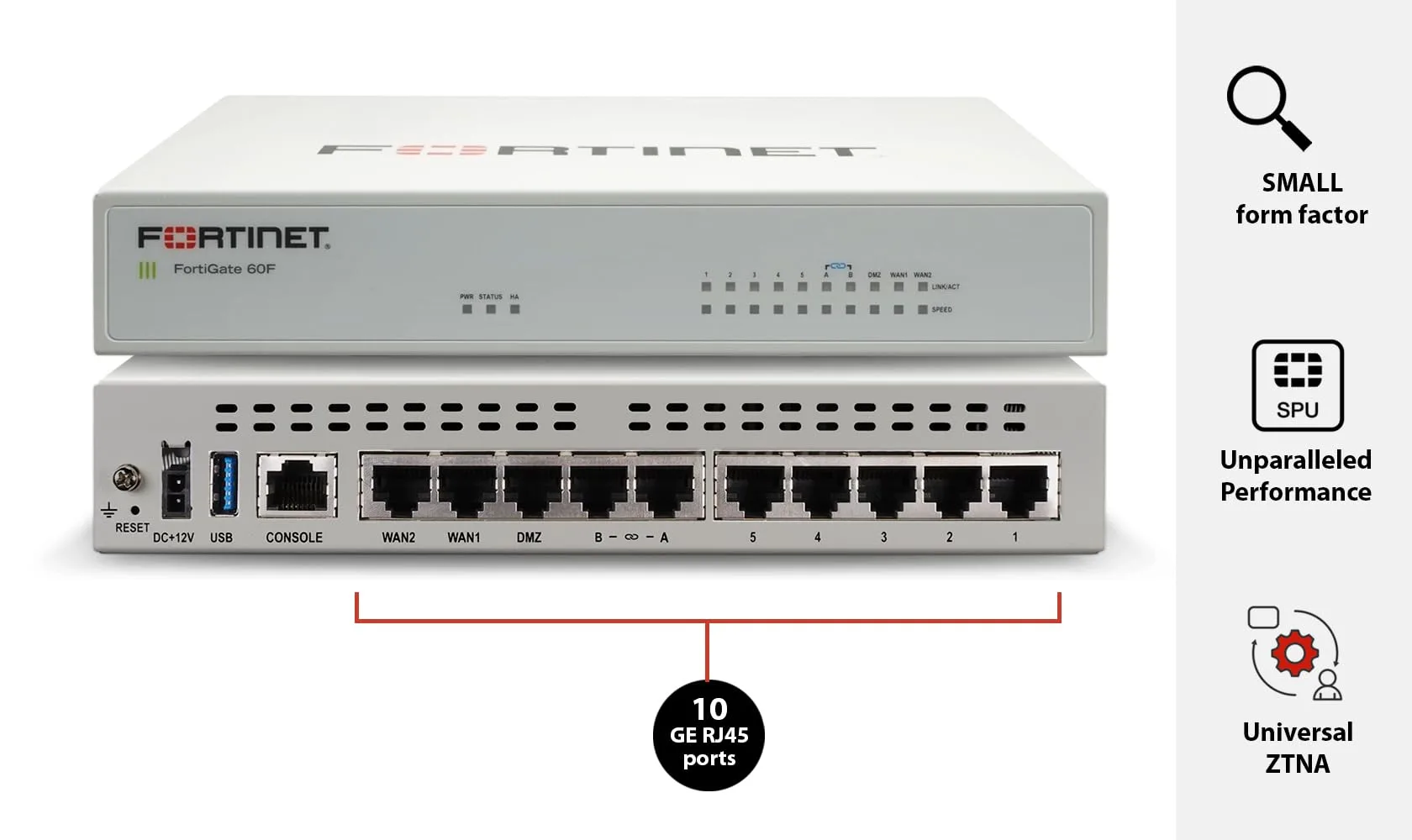
Network security relies heavily on clear visibility. When managing multiple firewalls, tracking every event across your

Opening Scene: When Seconds Matter in a Data BreachIt was early March 2026 when a major European financial institution p

What is the SOC 2 Compliance? The SOC 2 (System and Organization Controls 2) is a voluntary compliance standard of

Security Operations Centers (SOCs) play a critical role in protecting organizations from cyber threats. However, many SO

IntroductionAs we settle into 2026, privacy continues to be the fulcrum upon which the modern digital experience balance

In the fast-evolving world of cybersecurity, one question is increasingly being asked by both beginners and experienced