
Why Virtual Private Networks Remain Vital in an Increasingly Connected World
The Invisible Shield: Opening the VPN ConversationImagine a bustling city square where millions gather daily, exchanging
Privacy, infosec, hacking, data protection, VPNs
331 articles
The Invisible Shield: Opening the VPN ConversationImagine a bustling city square where millions gather daily, exchanging

When a business starts looking into ISO 27001 certification, the first question that often comes up is, "How much is thi

The Invisible Battlefield: Privacy’s Crucial Role Amid Rising Cyber ThreatsIn an era defined by hyperconnectivity, priva
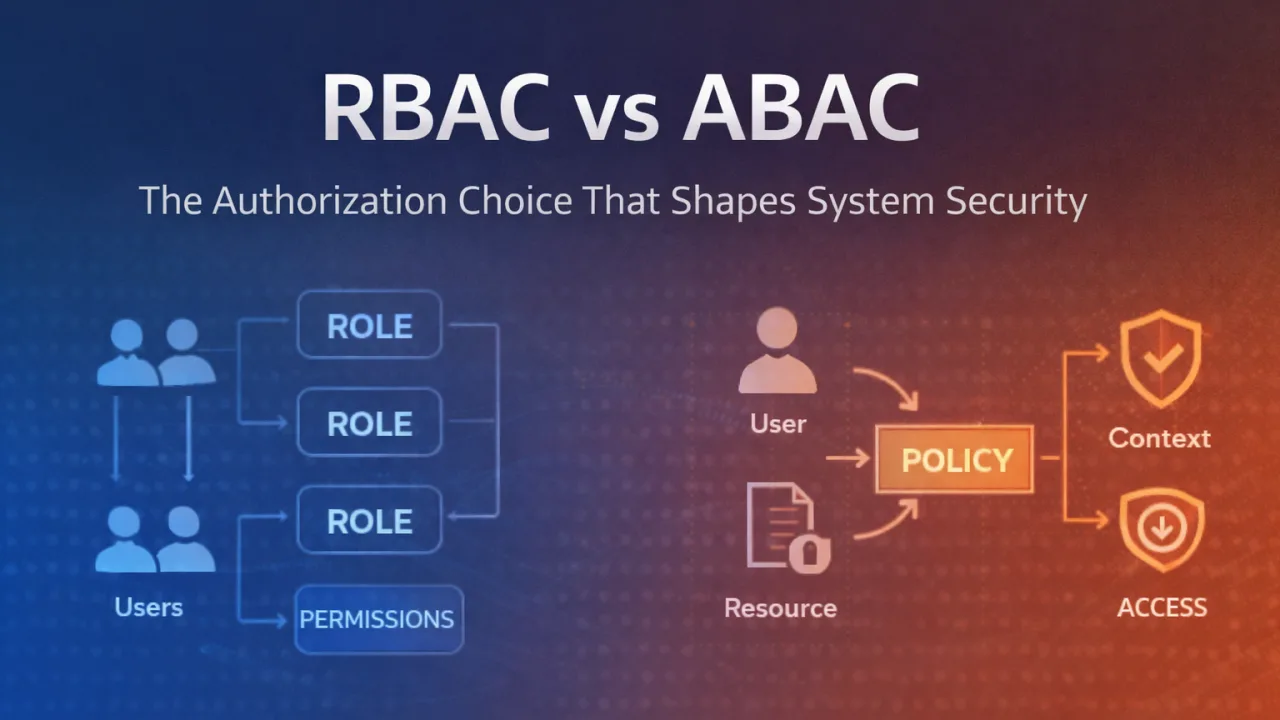
The prevention of fraud and data breach activities starts with strict access control strategies. Therefore, companies ne

The Invisible Battle: A Glimpse Into Hacking’s Pervasive InfluenceIn the early hours of a seemingly ordinary Tuesday in

The Unseen Crisis: A Glimpse into the Depths of a Data BreachOn a chilly morning in January 2026, a multinational conglo

In today’s rapidly evolving digital landscape, businesses must prioritize security to protect their sensitive data and s

The Rising Tide of Cyber Threats: A 2026 PerspectiveIn early 2026, a major multinational corporation suffered a sophisti

Cyber threats are evolving faster than most organizations can keep up. Whether you're running a mid-sized company or a F

In today's digital world, we spend most of our day jumping between different apps and websites. Whether you are working

With the rapid growth of digital businesses and online transactions, cybersecurity has become a top priority for organiz
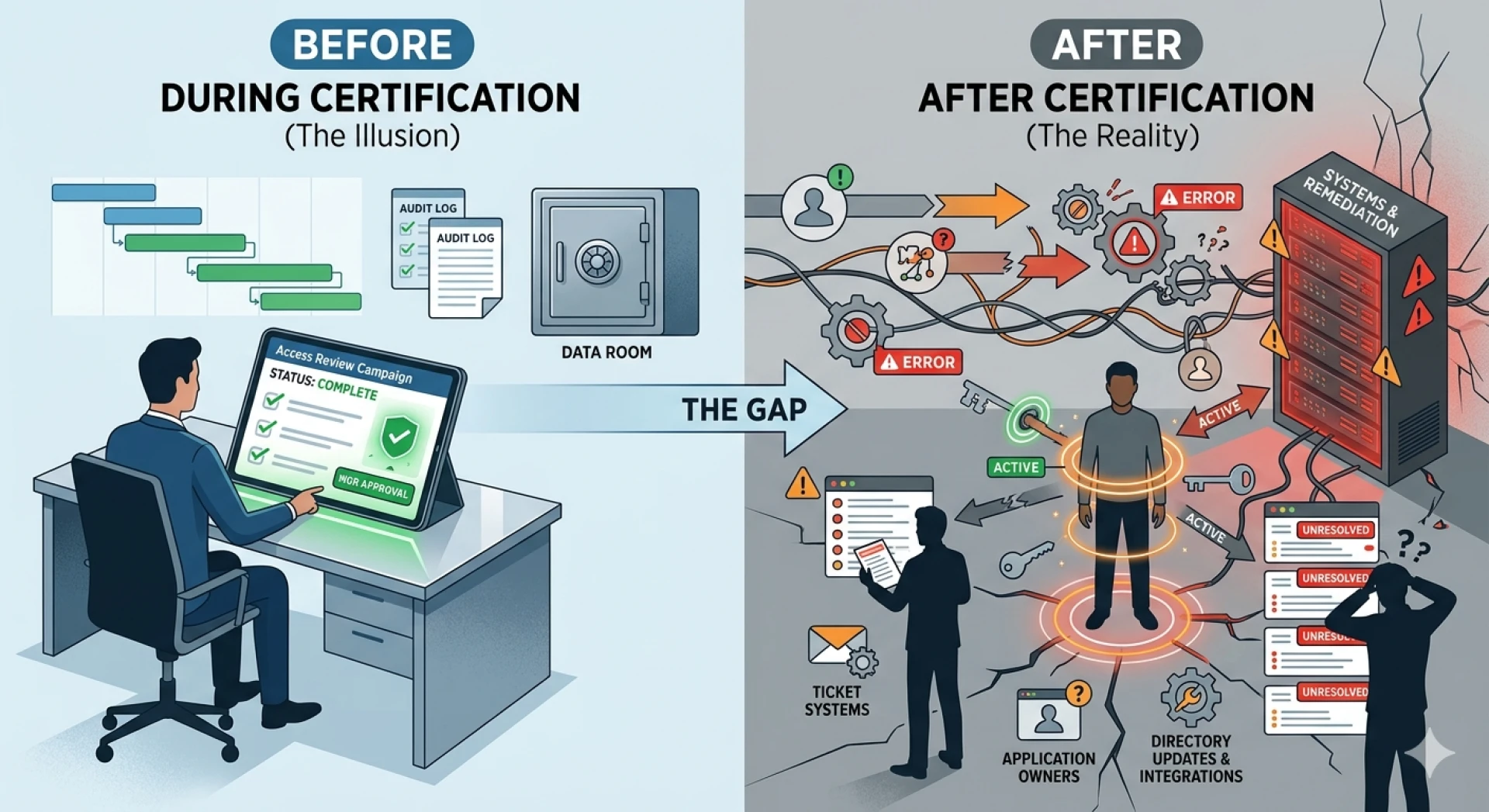
A split-screen illustration titled 'Before vs After Certification.' The left side shows a clean 'Complete' status on an

In Sikh tradition, Rumala Sahib holds deep spiritual significance as it is used to respectfully cover Sri Guru Granth Sa

In today’s digital-first environment, businesses are more connected than ever. While this brings convenience and efficie

In an era where cyber threats are constantly evolving, businesses must take proactive steps to protect their digital ass

In today’s digital-first world, cyber threats are growing rapidly, putting businesses of all sizes at risk. From data br

The digital landscape for East New York defense contractors has shifted from a "best effort" security model to a strict,
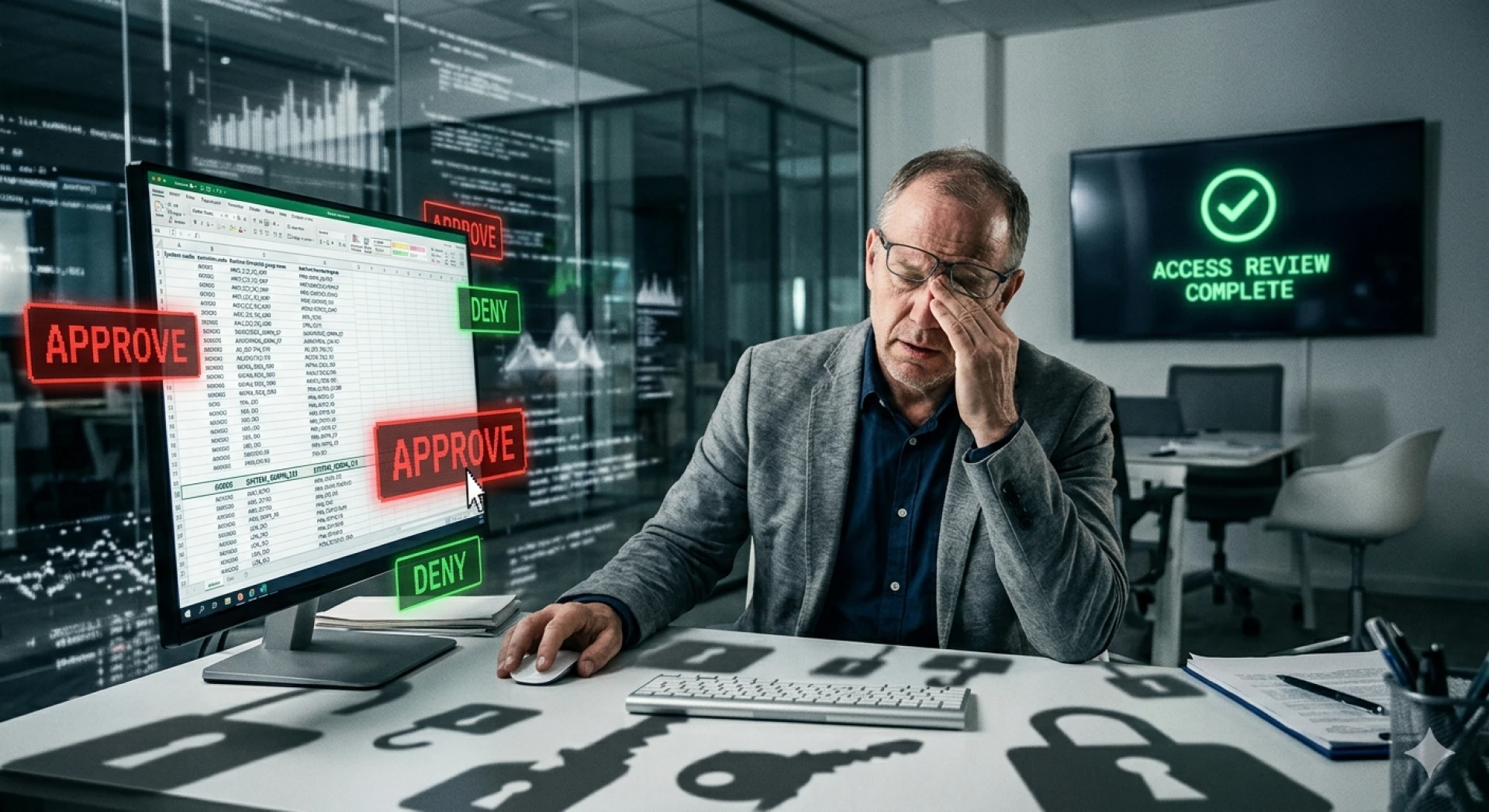
Why Your Access Review Is Lying to You (& How SaaS Made It Worse)

Cybersecurity is no longer optional—it’s a necessity. Whether you are a beginner or an experienced professional, using t

Modern businesses operate in a fast-paced digital environment where even a brief disruption can lead to significant fina

Discover trusted IT services Temecula businesses rely on for proactive support, cybersecurity, and scalable growth.
The internet has become an essential part of everyday life. From online banking and shopping to streaming, communication

The Modernization Assumption: Why Your IGA Program is Stalling
As businesses become more digital, the connection between cybersecurity and quality management systems is becoming impos